Blogs
Blogs
Essential Insights from Gartner's 2025 Managed Mobility Services Market Guide
Explore a preview of Gartner’s 2025 Market Guide for managed mobility services and download the full report to see how your company compares.
Blogs
How Sakon Fits Into the Future of Healthcare: An Interview With Jennifer Hutchinson, VP of Sales at Sakon
Discover how Sakon is revolutionizing healthcare IT and join us at HIMSS24 for an unforgettable experience!

Blogs
Key Takeaways from the 2023 Gartner® TEM Market Guide
Read the key takeaways from the 2023 Gartner® TEM Market Guide.
Press Releases
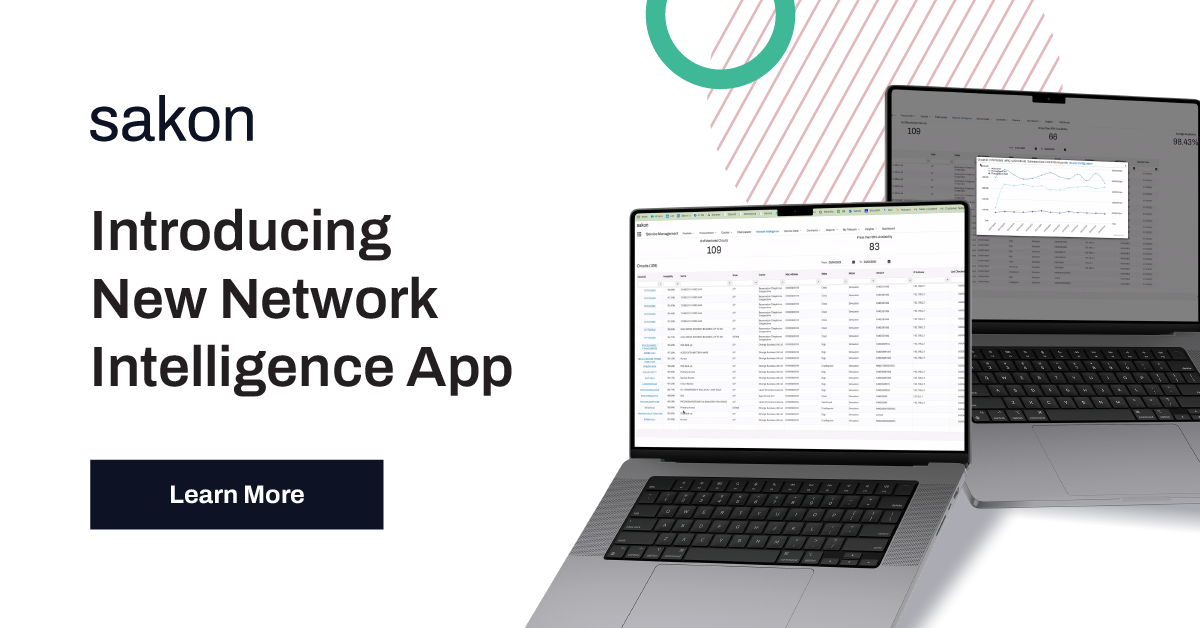
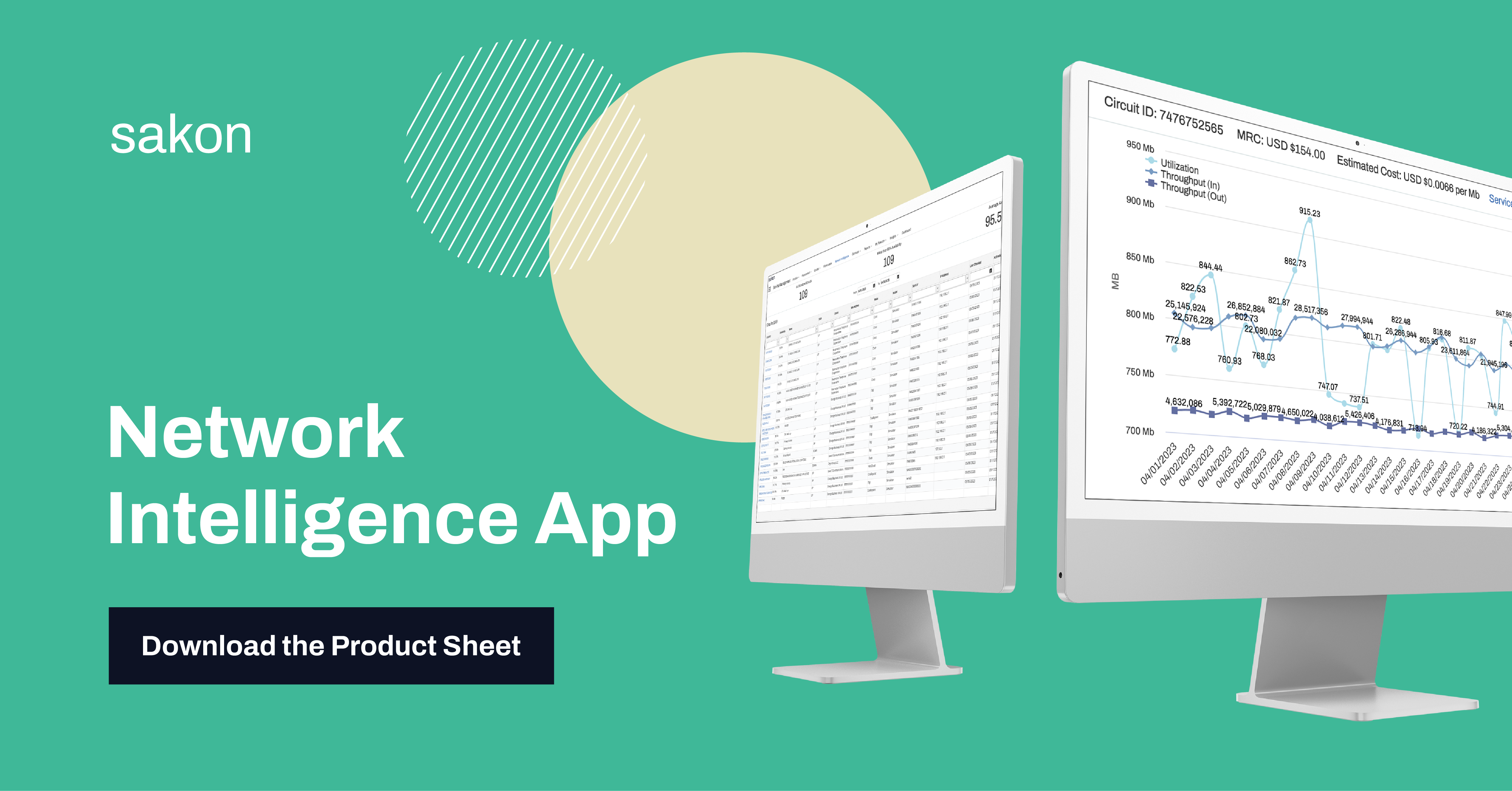
Sakon Introduces New Network Intelligence App
Sakon introduces a new network intelligence application that will transform the way enterprises manage their network infrastructure costs and performance.

Blogs
Fight Inflationary Pressures with IT Cost Optimization Strategies
Business costs are going up, learn how to fight inflationary pressures with our IT cost optimization strategies and telecom expense management.
Editor's Pick

TEM
Sakon Maintains its #1 Spot on Gartner Peer Insights for Telecom Expense Management
Discover how Sakon continues to excel in the telecom expense management industry with candid reviews from Gartner’s Peer...
Discover the resources that matter
Explore our blogs, case studies, and product insights instantly with our AI-powered search.
Ask a question or describe what you are looking forProduct Brief
View All
Product Sheet
Cloud Expense Management Product Brief
Press Release

Press Release
Sakon Renews AOTMP Key Certifications and Sponsorships
Sakon, a leading provider of Telecom Cloud solutions for expense management and lifecycle optimization, has renewed its Efficiency First® Solution Certification.

Press Release
Sakon Names Joe Fasanella Chief Revenue Officer to Lead Next-Phase Growth of the Intelligent Telecom Cloud
Sakon Names Joe Fasanella Chief Revenue Officer to Lead Next-Phase Growth of the Intelligent Telecom Cloud

Press Release
Jombay “1000 Women Leaders Program” Selects Member of Sakon Delegation for Top 10% Club
Jombay “1000 Women Leaders Program” Selects Member of Sakon Delegation for Top 10% Club
.png)
Press Release
Sakon Earns Industry-Leading Number of Finalist Spots in Jombay “1000 Women Leaders Program”
Sakon Earns Industry-Leading Number of Finalist Spots in Jombay “1000 Women Leaders Program”

Press Release
Sakon renews AOTMP® Efficiency First® Certification for Telecom Expense Management and Managed Mobility Services
Sakon pledges to continue advancing the industry by aligning its solution benefits with AOTMP® guiding principles for the Efficiency First® Solution Certification Program.
Press Release
View All
Press Release
Sakon Renews AOTMP Key Certifications an...
Sakon, a leading provider of Telecom Cloud solutions for expense management and lifecycle optimizati...

Press Release
Sakon Names Joe Fasanella Chief Revenue ...
Sakon Names Joe Fasanella Chief Revenue Officer to Lead Next-Phase Growth of the Intelligent Telecom...

Press Release
Jombay “1000 Women Leaders Program” Sele...
Jombay “1000 Women Leaders Program” Selects Member of Sakon Delegation for Top 10% Club
Guides
View AllSakon Impact Assessment Sakon Impact Assessment
Let Sakon show you the exact difference and cost savings our solutions can make for your business. Our value assessment will take your actual data and information and create a report that outlines proposed solut...
Case Studies


Case Studies
Scaling Mobility Automation for a Fortune 100 Aerospace and Defense Company Scaling Mobility Automation for a Fortune 100 Aerospace and Defense Company
Eliminated manual fulfillment, unified mobility data, and achieved over $1M in annual savings through Sakon’s Mobile Services Solutions.
Case Studies
Modernizing Mobility Management for a Growing Global Food and Veterinary Company Modernizing Mobility Management for a Growing Global Food and Veterinary Company
Streamlined global mobility operations, improved end-user experience, and sustained scalability through Sakon’s Mobile Services Solutions.


Case Studies
Transforming Mobility for a Global Food and Beverage Leader Transforming Mobility for a Global Food and Beverage Leader
Unified mobility operations, automated lifecycle management, and achieved over $1M in annual savings through Sakon’s Mobile Services Solutions.


Case Studies
The Modern State of Business Pay Solutions The Modern State of Business Pay Solutions
Discover how Sakon's business bill pay solutions helped Dollar Tree streamline invoice processing, avoid late fees, and manage telecom expenses efficiently.

-1.png)




-2.png)
